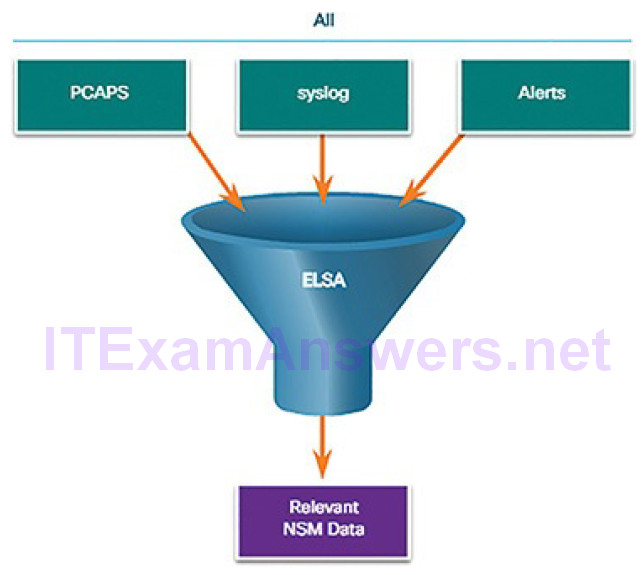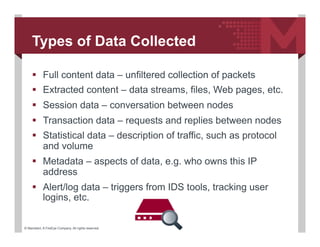
Intrusion Detection of NSM Based DoS Attacks Using Data Mining in Smart Grid – topic of research paper in Electrical engineering, electronic engineering, information engineering. Download scholarly article PDF and read for

Anomaly Detection Mechanism based on Common NSM Data Objects for Advanced Metering Infrastructure | Semantic Scholar

PDF) Anomaly Detection Mechanism based on Common NSM Data Objects for Advanced Metering Infrastructure | ACSIJ Journal - Academia.edu